Support Page Content
Phishing Awareness
Phishing attacks and cyber crimes continue to rise, and our goal is to empower you to identify, report, and not fall victim to digital scammers.
From 24/7 monitoring, ongoing education including periodic training exercises, university-wide use of Duo multi-factor authentication, advising you to use Global Protect VPN to access campus services, sending timely phishing alerts through SacSend, and resource sharing from the National Cybersecurity Alliance, we're committed to keeping our Hornet Family safe online!
Report Suspected Phishing
- Don't reply or click on any attachment or link, including any “unsubscribe” link (which could also be a malicious link)
- Report it so we can stop the threat as quickly as possible
- When you're done reporting, delete the message
Below are the main ways you can report a suspicious email, and other actions to take if you accidentally provided any information to a scammer.
You can quickly report a suspicious email directly through your university Outlook account by clicking PhishAlarm - which automatically generates a report to the IRT Information Security Office team. See our knowledge article for steps for different devices.
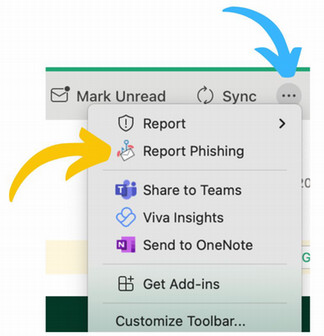
Where is it?
- Click on it in your (...) dropdown Outlook menu and select "Report Phishing," or
- Select "Customize Toolbar" from that dropdown menu to add the PhishAlarm icon directly to your Outlook ribbon header
- Open a new email message to "abuse@csus.edu"
- Drag and drop the suspicious message into the body of the new message as an attachment
- Add a subject line such as "possible phishing email" and click send
If you've clicked something in a phishing message and/or provided any credentials or information:
- Immediately change your SacLink account password at password.csus.edu, and then
- Alert the IRT Service Desk Team at servicedesk@csus.edu or (916) 278-7337
Types of Phishing
The National Cybersecurity Alliance offers a full library of topic-specific cybersecurity resources you can download - but in general, look for these tip-offs that what you've received may be a scam:
- Feels suspicious/out of left field. If you're not expecting this type of message, don't recognize the sender, or you've never received correspondence like it before.
- Urgent or emotionally appealing language or threats, to get you to act quickly.
- Unexpected attachments or vague links to "click here." Untrusted shortened URLs are another tip-off.
- Asks you to reply with personal/confidential/financial information, such as your ID or password, or to click a link to submit personal information.
- Email address doesn’t match the sender: for example, official Sac State communications will only come from @csus.edu email addresses. Careful though - addresses can be spoofed, so pay careful attention to the message content for clues.
- Generic email salutation instead of your name, or an incorrect recipient, or "Dear User."
- The “From” field has a .com, .org, or .net address, not a name ("Bob Smith") or specific group (“Office of the President”).
- Contains typos and grammatical errors
An advance-fee scam is a form of fraud and is one of the most common types of confidence tricks. The Federal Bureau of Investigation (FBI) defines an advance-fee scam as "when a victim pays money to someone in anticipation of receiving something of greater value - such as a loan, contract, investment, or gift - and then receives little or nothing in return."
The scam typically involves promises a victim a significant share of a large sum of money, in return for a small up-front payment, which the scammer claims will be used to obtain the large sum. When a victim makes the payment, the scammer either invents a series of further fees for the victim to pay or simply disappears.
Phishing schemes are correspondence designed to steal from you. They often look or sound official, with familiar logos or messaging, and will try to trick you into giving up information that can be later used in scams. We may open what we thought was a safe email, attachment or image only to find ourselves exposed to malware or a scammer looking for our personal data.
Phishing is more than just email, it's also arriving through:
- Phone calls (spoofed calls, voice phishing or "vishing"), and/or
- Text messages (SMS phishing or smishing)
A QR code (Quick Response Code) is a two-dimensional barcode that can store various types of data. It's often used for click-and-go access to websites, apps, or information when the user scans it with their smartphone camera.
QR code scams often send recipients to fake log in pages in order to steal their password. The messages/QR codes may promise discounts, rewards, or request personal or sensitive information. Scanning a QR code used in a phishing scam redirects users to a malicious website, or may even download malware onto their device. Be wary of this either in digital (or print) situations, such as job boards, event promotions, and more.
Unlike phishing, which is a broad net cast to large groups of people, spearphishing is a targeted attempt to steal your sensitive information through messages that appear to come from someone you may know. Spear-phishing attackers find their victims by scanning social networking sites and gathering an individual's email address, friends list, geographic location, and any posts about new gadgets that were recently purchased. The attacker then uses this information to act as a friend or a familiar entity and send a convincing but fraudulent message to their target asking them to open a malicious attachment or click on a link that takes them to a spoofed website to provide passwords, account numbers, PINs, and/or access codes. Spearfishing is the most successful form of acquiring confidential information on the internet, accounting for 91% of attacks.
Spoofing is when a scammer deliberately falsifies the information transmitted to your caller ID display to disguise their identity. Scammers often use spoofing numbers so it appears that an incoming call is coming from a local number, or spoof a number from a company or a government agency that you may already know and trust. If you answer, they use scam scripts to try to steal your money or valuable personal information, which can be used in fraudulent activity.
Digital Security Tools
Sacramento State requires all faculty, staff, and students to use 2-Step Verification with Duo, which provides extra account protection even if an attacker gains access to your password.
Global Protect VPN
As an additional security best practice, be sure to download and use Global Protect Virtual Private Network (VPN), which protects your connection whether on- or off-campus - and is especially important if you’re using an unsecure public Wi-Fi connection.
URL Defense
To protect campus users against malicious website links in emails, any link clicked from an email message will be filtered through two tools (Proofpoint and Microsoft Safe Links) which will verify whether a site is safe (you'll be connected) or is categorized as malicious and will be blocked (you'll receive a pop-up alert).
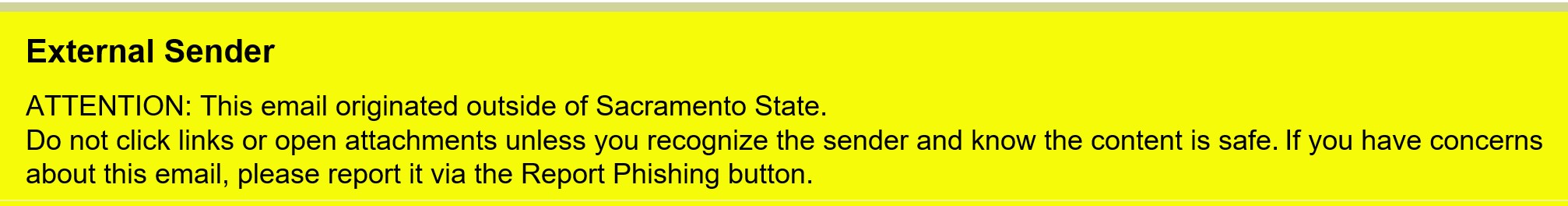
External Sender Email Banner
Incoming emails from outside campus (non @csus.edu addresses) feature an "External Sender" banner which can be helpful for staying alert and identifying unknown senders/potential threats.
Duo Flooding
 Multifactor authentication with Duo is a great protection against unauthorized access, but if your Sac State account becomes compromised, hackers may attempt to send you Duo push notifications you didn't originate in the hopes that you'll accept and allow them to gain access to campus systems as "you." If you receive a Duo push notification you did not originate, follow these steps:
Multifactor authentication with Duo is a great protection against unauthorized access, but if your Sac State account becomes compromised, hackers may attempt to send you Duo push notifications you didn't originate in the hopes that you'll accept and allow them to gain access to campus systems as "you." If you receive a Duo push notification you did not originate, follow these steps:
- Press the deny button, then click "yes" to report it as a suspicious login.
- Change your password ASAP to something completely different at password.csus.edu.
Internet of Things (IoT)
The Internet of Things (IoT) sounds Sci-Fi, but you know them as Alexa, your iPhone/Android, or a Ring front door camera. IoT devices interconnect our work and home worlds, and have truly become extensions of ourselves. Not securing them is what hackers count on when they try to steal your identity.
Brush up on these tips from the National Cybersecurity Alliance on how to lock down your devices:
NCSAM Month
Every October, Sacramento State serves as a champion of National Cybersecurity Awareness Month (NCSAM) which features educational campaigns, resources, and tips on how to out-trick hackers. Each week we shared topics through SacSend broadcast emails and social media to increase awareness to empower every Hornet to stay safe from phishing schemes. Here are 2024 campaigns:
- Week 1: 10/3 "Kickoff NCSAM month/Duo Flooding"
- Week 2: 10/10 "Fake Jobs"
- Week 3: 10/17 "Password Management"
- Week 4: 10/24 "Report Scams"
- Week 5: 10/31 "Happy Halloween/Topic Roundup"